TECHNOLOGY
What Is Data Loss Prevention Software? A Complete Guide to DLP Solutions for Modern Businesses

In today’s data-driven world, protecting sensitive information is no longer just a best practice—it’s a business imperative. From intellectual property to customer records, organizations are constantly at risk of data breaches, internal leaks, and regulatory penalties. That’s where data loss prevention software (DLP software) steps in.
This guide offers a comprehensive look at what DLP software is, why it matters, and how it can empower businesses to stay secure, compliant, and competitive.
What Is Data Loss Prevention Software?
Data loss prevention software is a digital security solution designed to identify, monitor, and protect sensitive information from unauthorized access, transfer, or misuse. It acts as a digital safeguard, preventing data from being leaked—whether through negligence or malicious intent—both inside and outside the organization.
In the modern workplace, where remote access and cloud-based platforms are standard, DLP software helps companies secure confidential data, boost productivity, and ensure compliance with global regulations. It gives organizations visibility and control over where their data goes and who interacts with it.
Key Features of Data Loss Prevention Software
Effective DLP software comes equipped with robust, intelligent features that not only protect data but also improve operational oversight:
Insider Threat Prevention
Employees—knowingly or unknowingly—are among the biggest risks to data security. DLP software identifies potentially harmful actions, such as copying sensitive files to USB drives or sending them to personal emails, and blocks them before damage is done.
Data Misconduct Detection
Automated systems flag and respond to abnormal data behavior. Whether it’s sudden access to high-value files or attempts to exfiltrate information, the software ensures violations don’t go unnoticed.
User Behavior Analytics
DLP tools monitor patterns in user activity and compare them against normal behavior. This enables early detection of threats and helps in refining internal policies.
Continuous Data Monitoring
DLP solutions work in real time, offering live monitoring of data in use, at rest, and in transit. This continuous oversight ensures that sensitive files are always under watchful eyes.
Employee Monitoring
Beyond cybersecurity, DLP software aids in employee productivity tracking—monitoring how users handle data, follow policies, and interact with systems, all within ethical boundaries.
These features collectively enhance organizational control, minimize risk, and empower managers to make informed security decisions.
Benefits of Using Data Loss Prevention Software
The adoption of data loss prevention software brings a multitude of advantages to businesses of all sizes and industries:
- Protection from Internal and External Threats: Whether the threat comes from a malicious insider or an accidental data leak, DLP tools act as a reliable defense line.
- Enhanced Data Visibility: Organizations gain real-time insights into how data flows across their network.
- Improved Productivity: Employees work more efficiently within secure systems, knowing policies are in place.
- Lower Legal and Financial Risks: Avoid costly data breaches, compliance fines, and reputational damage.
- Cultural Shift Toward Accountability: Knowing that activity is being monitored creates a more responsible and security-conscious workforce.
Compliance and Privacy Considerations
While DLP tools are essential for data protection, their deployment must respect employee privacy and align with local and international laws. Ethical usage means:
- Informing employees about monitoring practices.
- Setting transparent policies and usage boundaries.
- Complying with regulations like GDPR, HIPAA, CCPA, and more.
The goal is to strike a balance between safeguarding data and maintaining trust within the organization.
Real-World Use Cases Across Industries
Data loss prevention software is not one-size-fits-all. Its flexibility makes it valuable across a wide range of sectors:
- Healthcare: Protecting patient records under HIPAA while enabling secure access to data by authorized personnel.
- Finance: Monitoring for unauthorized access to customer financial data and preventing potential fraud.
- Education: Securing student information and intellectual property, especially in research-driven institutions.
- Tech & Software Development: Preventing the leak of proprietary code, algorithms, or product designs.
Each of these sectors faces unique challenges—and DLP tools are customized to meet their specific regulatory and operational needs.
How to Choose the Right DLP Software
Selecting the right DLP software requires a clear understanding of your organization’s priorities. Key factors include:
- Scalability: Choose software that grows with your company and adapts to new data challenges.
- Integrations: Ensure seamless compatibility with your existing tech stack (cloud platforms, CRM, email systems, etc.).
- User-Friendliness: Opt for a solution with intuitive dashboards, straightforward policy creation, and clear reporting.
- Vendor Support: Look for providers offering reliable customer support, training, and continuous updates.
Conducting a risk assessment and mapping your data flow is a critical first step before deciding on a DLP solution.
Implementing DLP Software: Best Practices
Introducing a DLP system into your organization requires a strategic approach:
- Assess Your Current Data Landscape – Understand what data needs protecting and where vulnerabilities exist.
- Develop Internal Policies – Define what constitutes misuse or unauthorized access.
- Involve Multiple Stakeholders – Collaborate with IT, legal, compliance, and HR departments.
- Train Employees – Provide clear guidelines and regular training to prevent accidental breaches.
- Continuously Review and Adapt – DLP implementation isn’t a one-time task; it must evolve with your business.
A well-executed rollout ensures smoother adoption and maximized ROI from your chosen DLP software.
Trends and the Future of DLP Software
As work becomes increasingly hybrid and decentralized, DLP software continues to evolve to meet new security demands. Key trends include:
- AI and Machine Learning Integration – Advanced pattern recognition and predictive threat detection.
- Cloud-Native DLP – Built-in solutions for platforms like Microsoft 365 and Google Workspace.
- Context-Aware Protection – Evaluating the sensitivity of data based on context before applying restrictions.
- Zero-Trust Security Models – Ensuring verification for every user and device accessing organizational resources.
These innovations will make DLP solutions more intelligent, efficient, and aligned with future-ready cybersecurity strategies.
Conclusion
In an age where data is both a valuable asset and a critical vulnerability, implementing robust data loss prevention software is no longer optional. It’s a foundational part of a smart, secure, and compliant business strategy.
By leveraging DLP software, companies not only prevent devastating data breaches but also foster a culture of accountability, ensure regulatory compliance, and safeguard their competitive edge.
As digital transformation continues, so too must our commitment to protecting what matters most—our data.
TECHNOLOGY
Glide to Productivity: The Rise of Noise-Reducing Air Casters

Modern industrial facilities are always searching for new solutions to increase operational efficiency while minimizing disruptions and safety hazards. Among the most promising innovations in recent years is the use of noise reducing casters, which harness compressed air to generate quieter, frictionless movement of heavy loads. As business demands continue to grow, maintaining high levels of productivity without sacrificing worker comfort or equipment longevity has become a top priority. Quiet, adaptable transport systems play an essential role in achieving this, allowing teams to focus on core tasks without the interruptions or safety risks that traditional wheeled casters can pose.
Understanding Air Casters
Air casters, also called air bearings, work by creating a thin cushion of air that allows objects to glide above the ground nearly effortlessly. When the compressed air is introduced to the caster, it fills a chamber and escapes through the bottom, producing a small air gap between the load and the floor. This nearly eliminates rolling resistance, allowing a few operators to reposition massive equipment with surprising ease. Their technology is applied across diverse industries, including manufacturing, logistics, and healthcare, making them an appealing alternative to conventional heavy-duty wheels.
Benefits of Noise-Reducing Air Casters
- Enhanced Safety: Air casters make it much easier for workers to mobilize heavy loads. They reduce the likelihood of strains, overexertion injuries, and mishaps that can occur with jerky or awkward movements. Their smooth offloading capabilities also reduce the risk of damage from sudden drops or collisions.
- Noise Reduction: Traditional hard-wheel casters often produce clattering and vibrations, especially on hard flooring. These noises can contribute to fatigue, interfere with communication, or even cause hearing-related issues over time. Air casters provide a calm, low-decibel solution ideal for environments where concentration and comfort are critical.
- Floor Protection: The air film produced by these casters spreads a load evenly across the floor surface instead of generating pressure points. This is crucial for facilities with sensitive, polished, or delicate flooring, as it helps maintain the longevity of expensive surfaces and reduces the need for frequent maintenance.
Applications Across Industries
The versatility of noise-reducing air casters makes them suitable for many different fields:
- Manufacturing: Industrial plants often require quick reconfiguration of machinery. With air casters, equipment can be repositioned rapidly and safely without shutting down production lines or causing workplace interruptions.
- Healthcare: Hospitals benefit from quieter transport solutions, using air casters to move heavy imaging machines and other vital equipment smoothly through patient areas without disruptive noises.
- Warehousing and Distribution: Distribution centers are embracing air casters for flexible inventory handling and efficient reconfigurations. This supports peak efficiency and responsiveness, especially during periods of high demand.
Implementing Air Casters in Your Facility
Successful integration of noise-reducing air casters requires careful planning. First, define the load requirements by determining the weight, size, and frequency of movement for your equipment. This ensures you select air casters with the right capacity and durability for your application. Next, evaluate your facility’s flooring. Smooth, level surfaces are ideal, but modern air caster systems can accommodate mild irregularities or be paired with temporary overlays in critical zones. Last, invest in staff training. Operators need to understand the proper use and routine upkeep of the casters to maximize performance and ensure longevity. Ongoing maintenance schedules should be created to check for leaks, wear, or other potential performance issues. For further guidance on workplace safety and ergonomics, consult resources like OSHA’s Ergonomics resources.
Future Trends in Air Caster Technology
The evolution of air caster design is ongoing. Newer models focus on increasing load capacities to handle even larger industrial equipment and refining energy efficiency for long-term operational savings. Many manufacturers are also integrating air casters with automated transport systems and robotics, which promise even further flexibility for just-in-time manufacturing and agile warehousing strategies. Staying up to date with these innovations enables companies to remain competitive and agile in a rapidly changing market landscape.
Environmental sustainability is also beginning to influence air caster manufacturing. Companies are experimenting with recyclable materials and designing components that lower overall resource consumption throughout the caster’s lifespan. As environmental regulations tighten across industries, air caster producers who prioritize green innovation will likely lead the sector.
Advanced data sensors are increasingly paired with air caster systems, enabling real-time performance tracking and predictive maintenance. These smart features offer facility managers valuable insights, such as identifying patterns of wear or pinpointing operational inefficiencies. Over time, this can drastically reduce unexpected downtime and repair costs by acting before failures occur. Such connectivity also allows seamless integration into broader facility management software, creating a truly connected, intelligent workplace.
Additionally, as workplace demographics evolve and a new generation of employees enters manufacturing and logistics, expectations for comfort, noise levels, and safety have never been higher. Noise-reducing air casters can help companies attract and retain skilled staff by providing cleaner, quieter working environments and reducing manual strain.
Looking ahead, industry analysts predict that remote and automated movement solutions, including air caster-based AGVs (automated guided vehicles), will soon become standard in factories, distribution centers, and hospitals. As the need for rapid, quiet, and error-free movement grows, facilities that transition early will position themselves as leaders in both innovation and employee satisfaction.
Conclusion
Noise-reducing air casters are driving substantial improvements in today’s material handling by offering safer, quieter, and more floor-friendly options for moving heavy objects. Their adoption is not only a testament to the progress of industrial innovation but a necessity for companies seeking to sustain high productivity standards and employee wellbeing. As technology advances, those who integrate noise-reducing air casters into their facilities will likely find themselves ahead in efficiency, workplace satisfaction, and overall operational excellence.
TECHNOLOGY
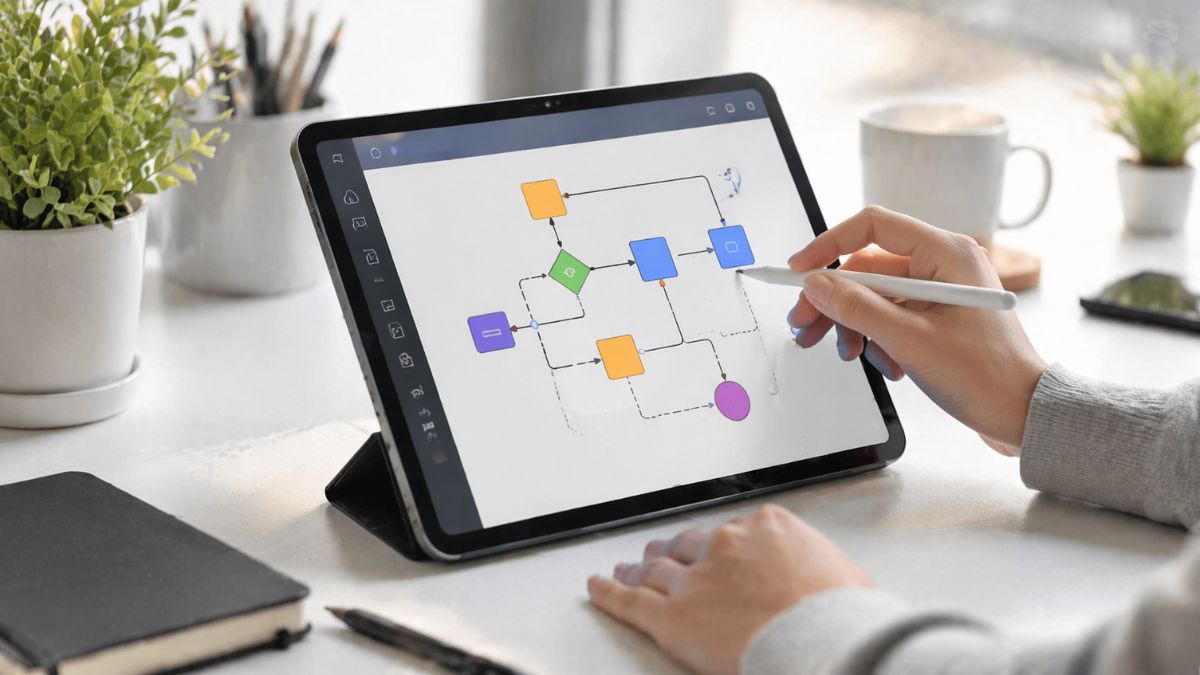
How to Create and Use a Diag Image for Better Visual Communication
Introduction
If you’ve ever struggled to explain a complex idea clearly, you’re not alone. This is where a diag image becomes incredibly useful. A diag image, short for diagram image, helps transform complicated information into easy-to-understand visuals. Whether you’re working on a blog post, presentation, or business report, using diagrams can dramatically improve clarity and engagement.
In today’s fast-paced digital world, people prefer scanning visuals over reading long blocks of text. That’s why integrating well-structured diagram images into your content is no longer optional—it’s essential.
What Is a Diag Image?
A diag image is a visual representation of information using shapes, lines, symbols, and structured layouts. It simplifies data, processes, or relationships into a graphical format that’s easier to understand.
Key Characteristics of a Diag Image
- Uses shapes like boxes, circles, and arrows
- Shows relationships or workflows
- Breaks down complex concepts
- Improves readability and retention
Common Types of Diagram Images
| Diagram Type | Purpose | Best Use Case |
|---|---|---|
| Flowchart | Shows process steps | Workflows, tutorials |
| Mind Map | Organizes ideas | Brainstorming, planning |
| Infographic | Combines data and visuals | Blog content, marketing |
| Organizational | Displays hierarchy | Company structure |
| Network Diagram | Shows connections | IT systems, relationships |
Why Diag Images Matter in Content Strategy
Using visual elements is not just about aesthetics—it directly impacts how your audience interacts with your content.
Boosts Engagement
Readers are more likely to stay on a page that includes visuals. Diagrams break monotony and keep users interested.
Improves Understanding
Complex ideas become easier when presented visually. For example, a step-by-step process is far clearer in a flowchart than in paragraphs.
Enhances SEO Performance
Visual content increases dwell time and reduces bounce rates, which are important ranking factors.
The Real Risks Of Driving Without Insurance In Nevada
How to Create an Effective Diag Image
Creating a powerful diagram isn’t just about drawing shapes. It requires clarity, structure, and purpose.
Step-by-Step Process
1. Define Your Goal
Ask yourself:
- What problem am I solving?
- Who is the audience?
2. Choose the Right Diagram Type
Different goals require different formats. For example:
- Use flowcharts for processes
- Use mind maps for ideas
3. Keep It Simple
Avoid clutter. Focus only on essential information.
4. Use Visual Hierarchy
Guide the viewer’s eye using:
- Size differences
- Color contrast
- Logical flow
5. Maintain Consistency
Use consistent shapes, colors, and fonts to create a professional look.
Best Tools for Creating Diag Images
There are many tools available, each with its own strengths.
Comparison of Popular Tools
| Tool Name | Best For | Ease of Use | Features |
|---|---|---|---|
| Canva | Beginners | Easy | Templates, drag-and-drop |
| Lucidchart | Professionals | Medium | Advanced diagramming |
| Draw.io | Free users | Medium | Custom diagrams |
| Visme | Marketing visuals | Easy | Infographics and charts |
| Figma | Designers | Advanced | Collaboration and UI design |
Practical Examples of Using Diag Images
Let’s explore how you can apply diagrams in real-life scenarios.
Blogging
- Explain processes like “How SEO Works”
- Visualize content strategies
Business Presentations
- Show growth charts
- Present workflows
Education
- Break down complex theories
- Illustrate concepts visually
Marketing
- Create engaging infographics
- Simplify product explanations
Pros and Cons of Using Diag Images
Advantages
- Makes content easier to understand
- Improves user engagement
- Enhances visual appeal
- Supports better memory retention
Disadvantages
- Can become cluttered if overused
- Requires time to design properly
- May confuse if poorly structured
Common Mistakes to Avoid
Even though diagrams are powerful, they can backfire if not used correctly.
Overcomplicating the Design
Too many elements can overwhelm the viewer.
Lack of Clear Flow
If the diagram doesn’t guide the reader logically, it loses its purpose.
Inconsistent Styling
Mixing different styles can make your content look unprofessional.
Ignoring Mobile Optimization
Ensure your diagrams are readable on smaller screens.
Best Practices for Using Diag Images
To get the most out of your visuals, follow these proven strategies.
Keep It Focused
Each diagram should communicate one main idea.
Use Color Strategically
Highlight key elements without overloading the design.
Add Context
Always explain the diagram briefly so users understand its purpose.
Optimize for SEO
- Use descriptive file names
- Add alt text
- Compress images for faster loading
Framework for Effective Diagrams
| Element | Best Practice | Outcome |
|---|---|---|
| Structure | Logical and sequential | Easy understanding |
| Design | Clean and minimal | Professional appearance |
| Content | Relevant and concise | Better engagement |
| Accessibility | Mobile-friendly and readable | Wider audience reach |
How Diag Images Improve User Experience
A well-designed diagram does more than just present information—it improves the overall experience.
Faster Information Processing
Visuals are processed quicker than text, helping users grasp ideas instantly.
Better Retention
People remember visuals more than plain text.
Increased Interaction
Users are more likely to share and engage with visual content.
Conclusion
A diag image is one of the most effective tools for simplifying complex information and enhancing user engagement. Whether you’re a blogger, marketer, or educator, incorporating structured diagrams into your content can make a noticeable difference.
By focusing on clarity, simplicity, and relevance, you can create visuals that not only look great but also deliver real value. Start small, experiment with different formats, and refine your approach over time.
FAQs
1. What is a diag image used for?
A diag image is used to visually represent complex information, making it easier to understand and communicate.
2. How do diag images improve SEO?
They increase engagement, reduce bounce rates, and improve dwell time, which positively affects search rankings.
3. What tools can I use to create diagram images?
Popular tools include Canva, Lucidchart, Draw.io, and Figma.
4. Are diag images suitable for blogs?
Yes, they help explain concepts clearly and make content more engaging.
5. How can I optimize diagram images for search engines?
Use descriptive file names, add alt text, and compress images for faster loading.
TECHNOLOGY
Be Creative: Using AI to Turn Your Imagination into Real-World 3D Objects
The traditional barrier to 3D creation has always been a steep technical curve. For years, turning a mental concept into a digital reality required mastering complex user interfaces, understanding vertex manipulation, and navigating non-intuitive sculpting tools. This “blank canvas” anxiety often stifled the very inspiration it was meant to capture. However, the rise of sophisticated generative tools is shifting the paradigm. By using a text to 3D mesh generator, creators can now bypass the mechanical drudgery of manual modeling and focus entirely on their creative vision.
From Word to Mesh: How Generative Logic Works
Transforming a descriptive prompt into a geometric structure is no longer a matter of simple surface estimation. Modern pipelines rely on Native volumetric logic to ensure that the internal mathematical foundation of a model is sound. Unlike older methods that often produced hollow shells or distorted geometry, this approach treats the object as a solid entity from the start.
The Direct3D-S2 architecture allows the system to interpret high-level text commands and translate them into a high-resolution grid. This ensures that when you describe a “medieval iron lantern with intricate filigree,” the AI isn’t just drawing a picture; it is calculating the specific volume and depth required to make that object functional in a 3D space.
Refining the Vision with Neural4D-2.5
True creativity requires iteration. A first draft is rarely the final masterpiece, which is why the “Conversational Architect” workflow is a game-changer for designers. Through the Neural4D-2.5 multi-modal model, you can engage in a dialogue with your creation.
If the generated mesh is too thick or the textures feel off, you simply tell the AI to “sharpen the edges” or “apply a brushed copper PBR material.” The system then adjusts the edge flow and PBR textures according to your natural language instructions. This process ensures deterministic output, giving you precise control over the final result rather than forcing you to settle for a randomized guess.
🎯 Practical Applications for the Inspired Creator:
⚡ 3D Printing: Generate watertight STL files that are mathematically closed and ready for your slicer software without manual hole-patching.
⚡ Game Design: Build engine-ready props, environmental assets, or NPCs that feature clean topology for instant integration into Unity or Unreal.
⚡ Digital Art: Use specialized AI Anime styles to create personalized VRM avatars or stylized backgrounds for webcomics and illustrations.
Technical Checklist for High-Quality Output
To get the most out of your creative session, focus on these technical pillars:
✅ Prompt Specificity: Use clear, descriptive language to help the Direct3D-S2 engine identify core geometric features.
✅ Texture Selection: Enable AI Texture generation to ensure your model includes native Normal, Roughness, and Metallic maps for realistic light reaction.
✅ Export Formats: Select .fbx or .obj to ensure seamless pipeline integration with standard industry software.
Your Inspiration, Accelerated
Creativity is about the journey from “thought” to “thing.” By removing the friction of technical modeling, AI allows us to return to the core of design: the idea itself. Whether you are a hobbyist looking to print a custom miniature or a professional designer rapidly prototyping a new product line, the focus should always be on quality and creative freedom. Stop fighting the software and start building with tools that turn your imagination into a tangible, high-fidelity reality.
-

 TOPIC8 months ago
TOPIC8 months agoTop 5 Features of Googlediqiu You Didn’t Know About
-

 TOPIC1 year ago
TOPIC1 year agoWhy Large Waterproof Outdoor Rugs Are Essential for All Outdoor Spaces
-

 TOPIC1 year ago
TOPIC1 year ago7 Expert Tips For Choosing The Best Basement Renovation Companies
-

 FASHION1 year ago
FASHION1 year agoHow to Layer Your White Dress for Cold Weather?
-

 TOPIC10 months ago
TOPIC10 months agoWhy Greece Katz Martian Has Everyone Talking in 2025
-

 BUSINESS11 months ago
BUSINESS11 months agoTop 5 Features of Sowix Online That Every User Should Know About
-

 TOPIC11 months ago
TOPIC11 months agoTop Features of BetterThisWorld .com You Need to Know About
-

 FINANCE1 year ago
FINANCE1 year agoHow TraceLoans Can Simplify Your Finances
